When I wrote a Home Lab update post back in January 2020, I talked about AI being one of the technologies that I wanted to focus on in my home lab.
At that time, AI had unlimited possibilities but was hard to work with. Frameworks like PyTorch and Tensorflow existed, but they required a Python programming background and possibly an advanced mathematics or computer science degree to actually do something with them. Easy-to-deploy self-hosted options like Stable Diffusion and Ollama were still a couple of years away.
Then the rest of 2020 happened. Since I’m an EUC person by trade, my attention was diverted away from anything that wasn’t supporting work-from-home initiatives and recovering from the burnout that followed.
GPU accelerated computing and AI were starting to come back on my radar in 2022. We had a few cloud provider partners asking about building GPU-as-a-Service with VMware Cloud Director.
Those conversations exploded when OpenAI released their technical marvel, technology demonstrator, and extremely expensive and sophisticated toy – ChatGPT. That kickstarted the “AI ALL THE THINGS” hype cycle.
Toy might be too strong of a word there. An incredible amount of R&D went into building ChatGPT. OpenAI’s GPT models are an incredible technical achievement, and it showcases the everyday power and potential of artificial intelligence. But it was a research preview that people were meant to use and play with. So my feelings about this only extend to the free and public ChatGPT service itself, not the GPT language models, large language models in general, or AI as a whole.
After testing out ChatGPT a bit, I pulled back from AI technology. Part of this was driven by trying to find use cases for experimenting with AI, and part of it was driven by an anti-hype backlash. But that anti-hype backlash, and my other thoughts on AI, is a story for another blog.
Finding my Use Case
Whenever I do something in my lab, I try to anchor it in a use case. I want to use the technology to solve a problem or challenge that I have. And when it came to AI, I really struggled with finding a use case.
At least…at first.
But last year, Hasbro decided that they would burn down their community in an attempt to squeeze more money out of their customers. I found myself with a growing collection of Pathfinder 2nd Edition and 3rd-party Dungeons and Dragons 5th Edition PDFs as I started to play the game with my son and some family friends. And I had a large PDF backlog of other gaming books from the old West End Games Star Wars D6 RPG and Battletech.
This started me down an AI rabbithole. At first, I just wanted to create some character art to go along with my character sheet.
Then I started to design my own fantasy and sci-fi settings, and I wanted to create some concept art for the setting I was building. I had a bit of a vision, and I wanted to see it brought to life.
I tried Midjourney first, and after a month and using most of my credits, I decided to look at self-hosting options. That led me to Stable Diffusion, which I tested out on my Mac and my Windows desktop.
I had a realization while trying to manage space on my Macbook. Stable Diffusion is resource heavy and can use a lot of storage when you start experimenting with models. The user interfaces are basically web applications built on the Gradio framework. And I had slightly better GPUs sitting in one of my lab hosts.
So why not virtualize it to take advantage of my lab resources? And if I’m going to virtualize these AI projects, why not try out a few more things like using an LLM to talk to my game book PDFs.
My Virtual AI Lab and Workloads
When I decided to build an AI lab, I wanted to start with resources I already had available.
Back in 2015, I convinced my wife to let me buy a brand new PowerEdge R730 and a used NVIDIA GRID K1 card. I had to buy a brand new server because I wanted to test out the brand new (at the time) GPU virtualization in my lab VDI environment, and the stock servers were not configured to support GPUs. GPUs typically need 1100 watt power supplies and an enablement kit to deliver power to the GPU that aren’t part of the standard server BOM. Most GPUs that you’d find in a data center are also passively cooled, so the server needs high CFM-fans and hi-speed fan settings to increase airflow over them.
That R730 has a pair of Intel E5-2620 v3 CPUs, 192GB of RAM, and uses ESXi for the hypervisor. Back in 2018, I upgraded the GRID K1 card to a pair of NVIDIA Tesla P4 GPUs. The Tesla P4 is basically a data center version of a GTX 1080 – it has the same GP104 graphics processor and 8GB of video memory (also referred to as framebuffer) as the GTX 1080. The main differences are that it is passively cooled and it only draws 75 watts, so it can draw all of its power from the PCIe slot without any additional power cabling.
My first virtualized AI workload was the Forge WebUI for Stable Diffusion. I deployed this on a Debian 12 VM and used PCI passthrough to present one of the P4 cards to the VM. Image generation times were about 2-3 minutes per image, which is fine for a lab.
I started to run into issues pretty quickly. As I said before, P4 only has 8GB of framebuffer, and I would start to hit out-of-memory errors when generating larger images, upscaling images, or attempting to use LORAs or other fine-tuned models.
When I was researching LLMs, it seemed like the P4 would not be a good fit for even the smallest models. It didn’t have enough framebuffer, poor fp16 performance, and no support for flash attention. So the P4 gives an all-around bad experience.
So I decided that I need to do a couple of upgrades. First, I ordered a brand new NVIDIA L4 datacenter GPU. The L4 is an Ada Lovelace generation datacenter GPU. It’s a single-slot, 24GB of framebuffer GPU that only draws 75 watts. It’s the most modern evolution of the P4 form factor.
But the L4 took a while to ship, and I was getting impatient. So I went onto eBay and found a great deal on a pre-owned NVIDIA Tesla T4. The T4 is a Turing generation datacenter GPU, and it is the successor to the P4. It has 16GB of framebuffer, and most importantly, it has significantly improved performance and support for features like flash attention. And it also only draws 75 watts.
The T4 and L4 were significant improvements over the P4. I didn’t do any formal benchmarking, but image generation times went from 2-3 minutes to less than a minute and a half. And I was able to start building out an LLM lab using Ollama and Open-WebUI.
What’s Next
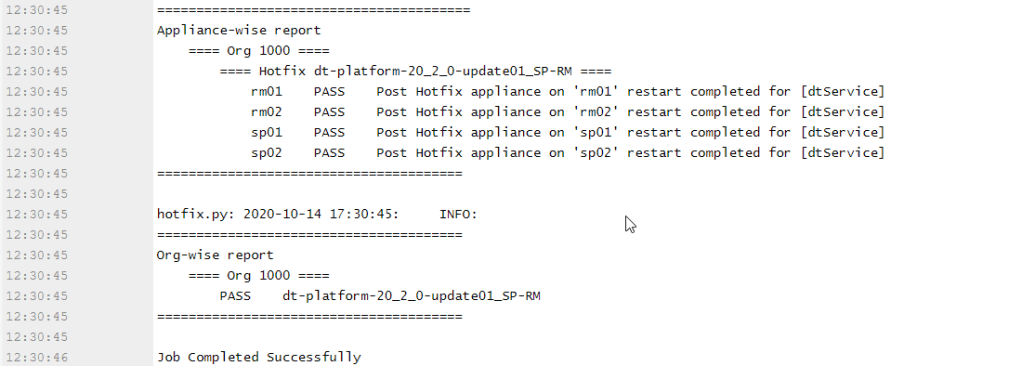
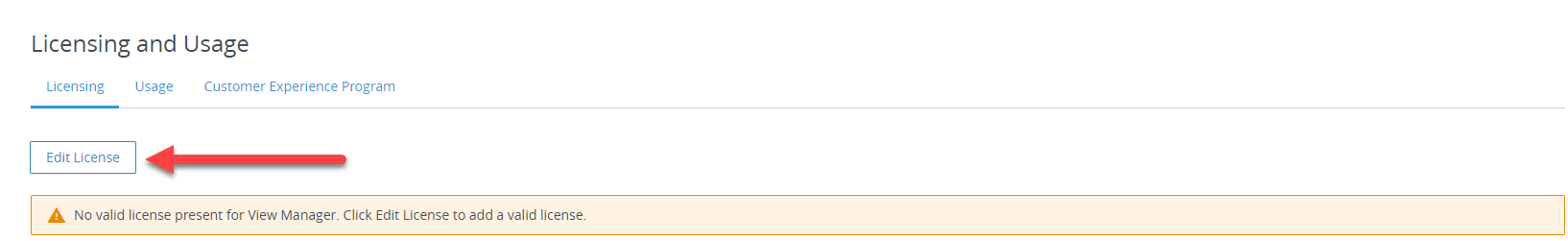
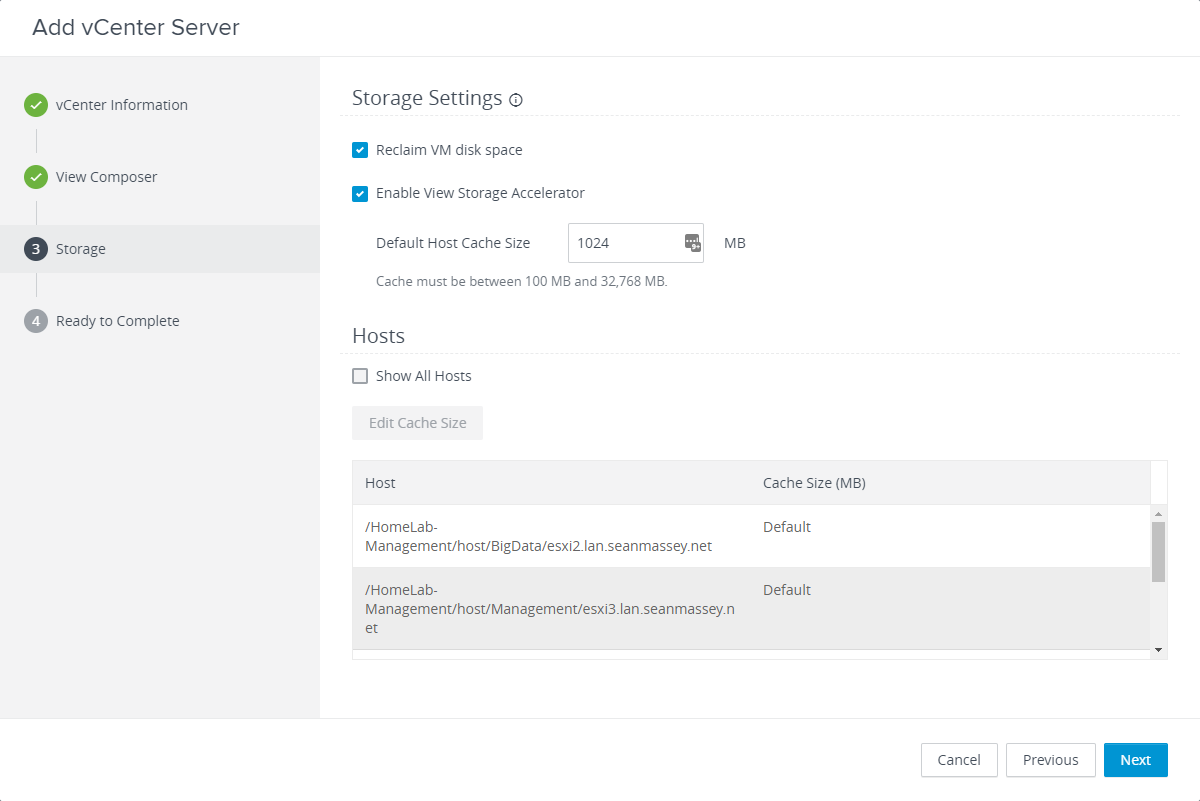
The initial version of this lab used PCI Passthrough to present the GPUs to my VMs. I’m now in the process of moving to NVIDIA AI Enterprise (NVAIE) to take advantage of vGPU features. NVIDIA has provided me with NFR licensing through the NGCA program, so thank you to NVIDIA for enabling this in my lab.
NVAIE will allow me to create virtual GPUs using only a slice of the physical resources as some of my VMs don’t need a full GPU, and it will allow me to test out some different setups with services running on different VMs.
I’m also in the process of building out and exploring my LLM environment. The first iteration of this is being built using Ollama and Open-WebUI. Open-WebUI seems like an easy on-ramp to testing out Retrieval Augmented Generation (RAG), and I’m trying to wrap my head around that.
I’m building my use case around Pathfinder 2nd Edition. I’m using Pathfinder because it is probably the most complete ruleset that I have in PDF form. Paizo, the Pathfinder publisher, also provides a website where all the game’s core rules are available for free (under a fairly permissive license), so I have a source I can scrape to supplement my PDFs.
This has been kind of a fun challenge as I learn how to convert PDFs into text, chunk them, and import them into a RAG. I also want to look at other RAG tools and possibly try to build a knowledge graph around this content.
This has turned into fun, but also frustrating at times, project. I’ve learned a lot, and I’m going to keep digging into it.
Side Notes and Disclosures
Before I went down the AI Art road, I did try to hire a few artists I knew or who had been referred to me. They either didn’t do that kind of art or they didn’t get back to me…so I just started creating art for personal use only. I know how controversial AI Art is in creative spaces, so if I ever develop and publish these settings commercially, I would hire artists and the AI art would serve as concept art.
In full disclosure, one of the Tesla P4s was provided by NVIDIA as part of the NGCA program. I purchased the other P4.
NVIDIA has provided NFR versions of their vGPU and NVAIE license skus through the NGCA program. My vSphere licensing is provided through the VMware by Broadcom vExpert program. Thank you to NVIDIA and Broadcom for providing licensing.






















































You must be logged in to post a comment.